Do you know what your API’s are doing? First, lets start off with understanding what API security is. According to Fortinet.com, application programming interface (API) security is the practice of preventing or mitigating attacks on API’s. API’s are critical to protect the sensitive data being transferred. API’s transfer sensitive data between users, API’s and the apps and systems they interact with. Insecure API’s can be an attackers dream.
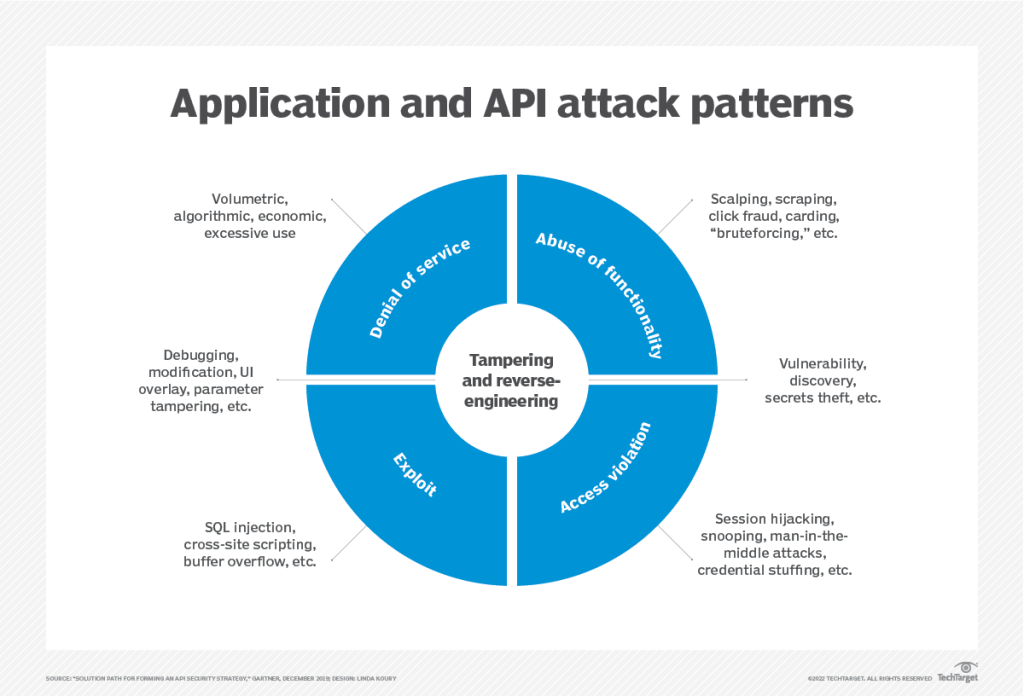
There are a number of attacks that can be performed on API’s which include: Man-in-the-Middle (MITM), Distributed denial-of-service (DDoS), injections and broken access control. By knowing and understanding this and your API risks, one can help reduce their chances of being affected.
Listed below are the TOP 10 API security risks:
- Broken objective-level authorization (BOLA) – this risk allows users to access or modify data the requestors shouldn’t have access to.
- Broken function-level authorization- this risk occurs when principles of least privilege is not implemented.
- Broken user authentication- this risk occurs when an authentication process is compromised; an attacker can pose as another user on a one time or even permanent basis.
- Excessive data exposure- this risk occurs when API responses often return more data that is relevant or necessary; leading to an exposure of sensitive data as well.
- Improper assess management- this risk occurs when documentation is often omitted in the rush to release or update API’s, this leads to exposed or ghost endpoints.
- Lack of resources and rate limiting- this risk occurs when API endpoints are usually open to the internet and there are no restrictions on the number or size of the requests, which leads to a DoS and a brute force attack.
- Injection flaws- this risk occurs when rejects are not parsed and validated correctly; attackers can potentially launch a command or SQL injection attack to access it or execute malicious commands without authorization.
- Mass assignment- this risk happens when all data received from an online form is put into a database or object with just one line of code; this removes the need to write repetitive lines of form mapping code. Also, if the data is not specified as acceptable then, various attacks can occur.
- Security misconfiguration- this risk occurs when unsecure default configurations, incomplete or ad-hoc configurations, open cloud storage, misconfigured HTTP headers, unnecessary HTTP methods, permissive Cross-Origin Resource Sharing (CORS) and verbose error messages contain sensitive information.
- Insufficient Logging and Monitoring- this risk occurs when missing or ineffective integration with incident response, allow attackers to further attack systems, maintain persistence, pivot to more systems to tamper with and extract or destroy data.
So what can be done to help reduce your organizations API risk? One can follow the best practices below to help reduce their unintentional exposure to attackers.
Best Practices:
Vulnerabilities– with vulnerabilities, one could identify weak points in the API lifecycle.
Tokens– with tokens, one could require authentication of a token on either side of a
communication.
Encryption– with encryption, one could only allow the communication if a proper decryption
key is used.
OAuth and OpenID Connect– with OAuth and OpenID, one could require both to transfer information with
proper credentials.
Throttling and Quotas– with throttling and quotas, one could implement limits on throttle and quota to
help reduce attacks.
API gateway– with API gateway, one could implement one and authenticate it.
Zero-trust approach– with a zero-trust approach, one could ensure users are authenticated and trust no traffic regardless of where it comes from (within the network or outside the network).
Test API’s regularly– with testing API’s regularly, one could help ensure the right controls are in place and that the API’s are functioning correctly.
Stash your API keys– with stashing API keys, one could help identify and verify access to apps or sites that call an API.
Add monitoring– when adding monitoring to API’s, one could implement API monitoring and threat detection to be alerted on any abnormal behavior of the API’s.
In conclusion, there are many risk with the use of any technology. By following the best practices one will not be 100% protected but, they will be better protected than someone not using any of the above best practices as well as others on API’s. Since API’s are still pretty new to the cloud environment for many, testing them regularly will help you see other issues within them and allow one to fix the issues that come about. With effective monitoring, authenticating and encrypting one can limit how data is accessed and help ensure it can only be sent to and viewed by someone with authorization. Knowing this, who does not want to go back and check on their API’s to ensure they are functioning as expected and that they are being better protected.
References:
https://owasp.org/www-project-api-security/
https://www.fortinet.com/resources/cyberglossary/api-security
https://www.techtarget.com/searchapparchitecture/tip/10-API-security-guidelines-and-best-practice

